GitLab + Doppler CLI
Bring new features and workflows to how you manage GitLab CI/CD variables with Doppler.
In this guide, you'll learn how to use the Doppler CLI to inject secrets as environment variables into your scripts and commands.
Prerequisites
You have a GitLab repository with permissions for viewing and modifying CI / CD job variables
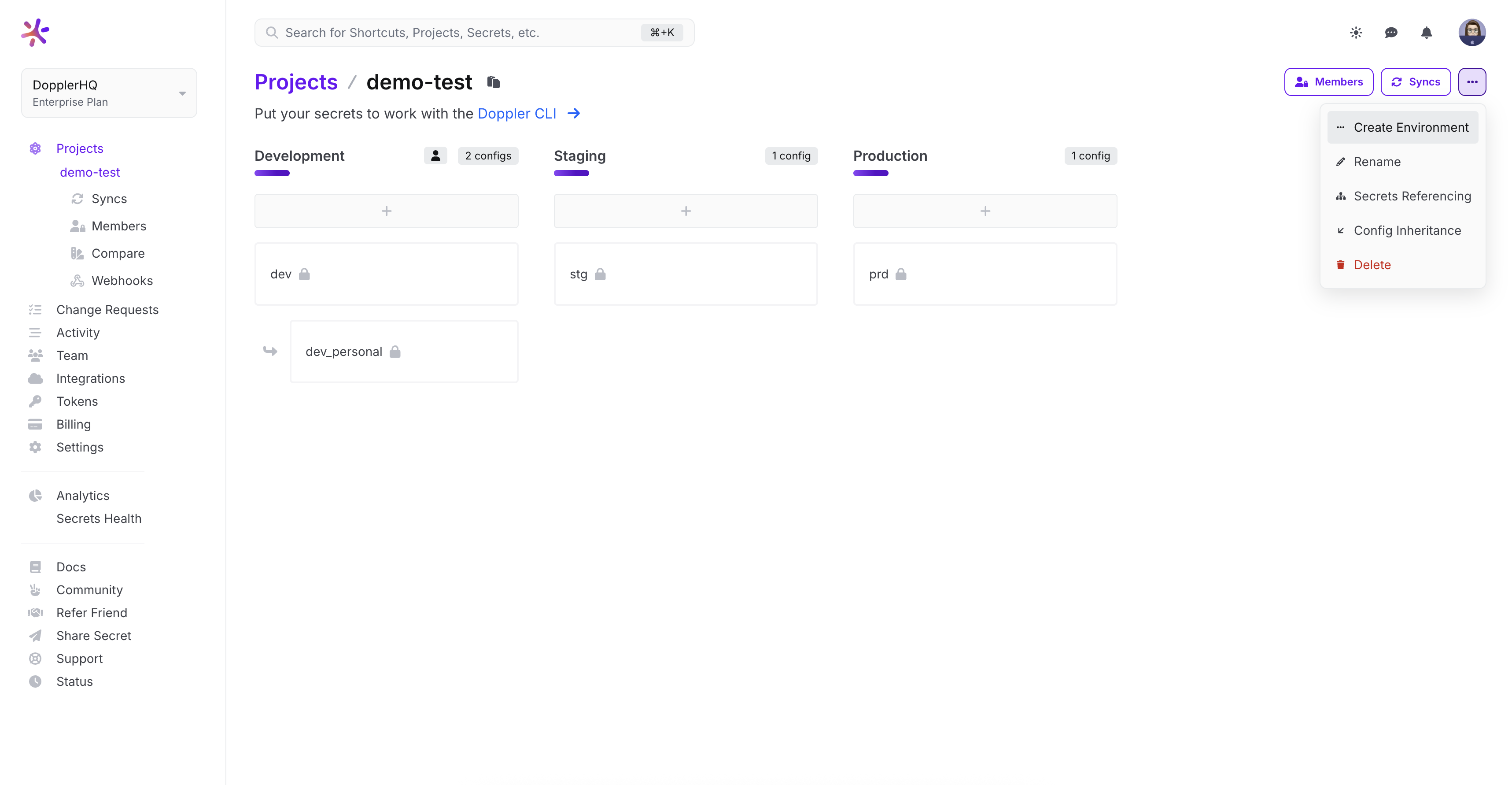
Doppler Project
Create a Doppler Project with a custom GitLab environment.
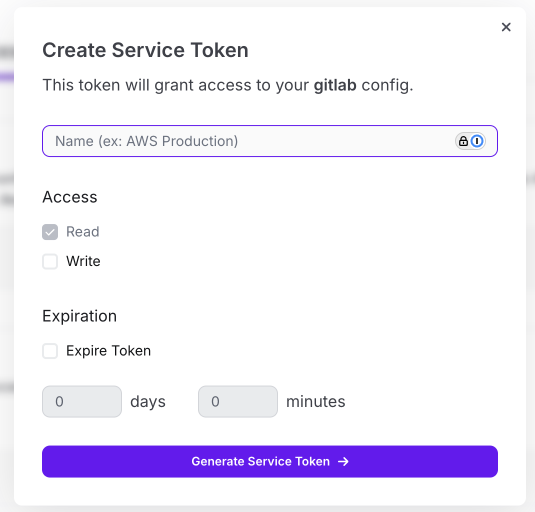
Service Token
Create a Service Token for the GitLab environment to provide the Doppler CLI with read-only secrets access and copy the Service Token value.
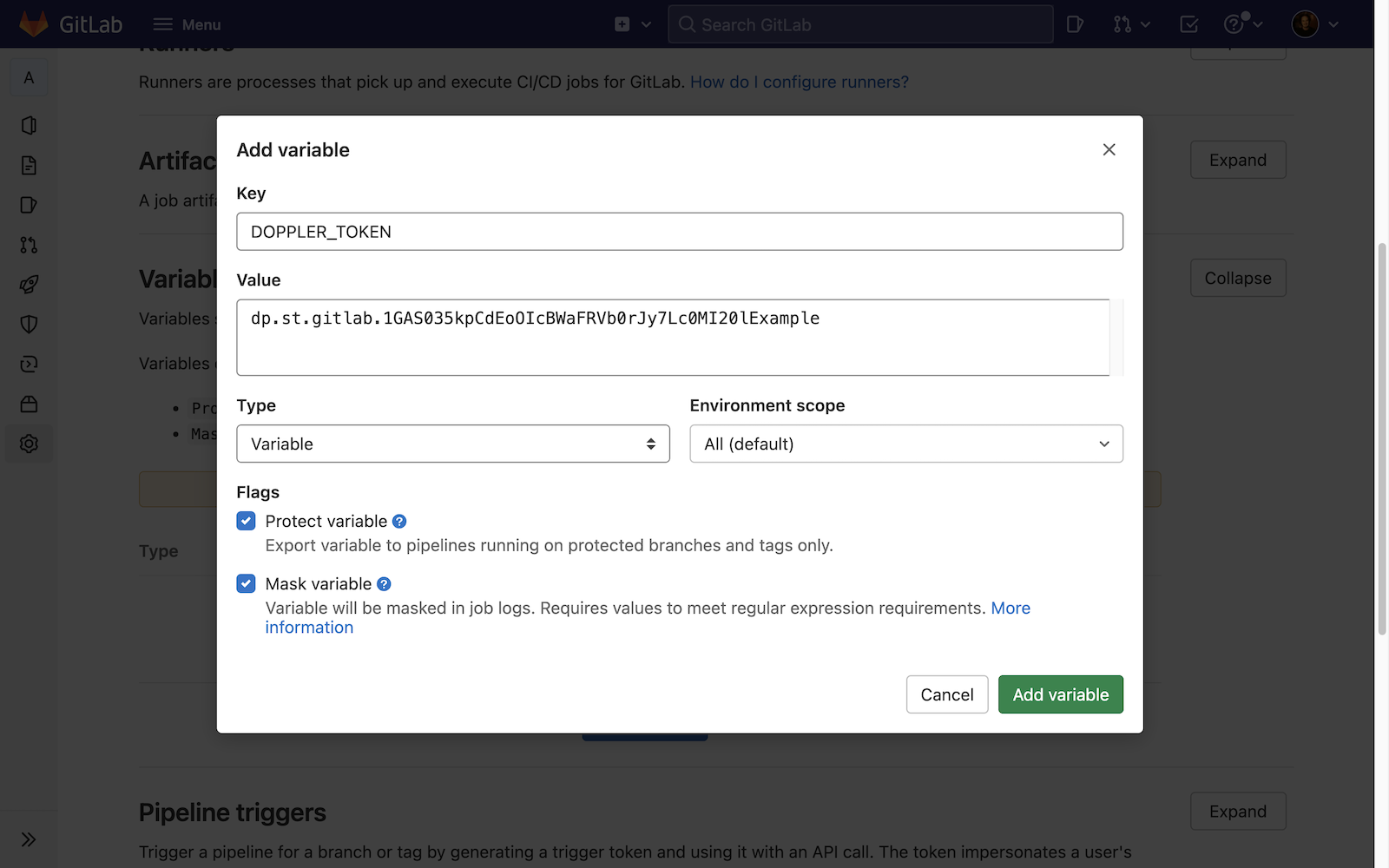
In GitLab, go to Settings > CI/CD > Variables and create a new DOPPLER_TOKEN variable with the Service Token value.
Configure Pipeline
Update your .gitlab-ci.yml to install the Doppler CLI and use doppler run to inject secrets as environment variables into any script or command:
image: ubuntu
build:
stage: build
script:
- apt update && apt install -y curl gnupg
- curl -Ls --tlsv1.2 --proto "=https" --retry 3 https://cli.doppler.com/install.sh | sh
- doppler run -- ./bin/build.sh
Amazing Work!Now you know how to configure GitLab CI / CD jobs to fetch secrets from Doppler.
Updated 9 months ago
