AWS Postgres Rotation
With automated secrets rotation, Doppler updates the password for a Postgres user at the interval you define. There's no need expose your database to the internet and Doppler will never require direct access to your database.
Requirements
Requires an upgraded subscriptionThis feature is exclusive to our Enterprise Plan. Book a demo to see it in action.
- Understand the Doppler rotation methodology, especially the two secret strategy
- Ability to create Postgres users
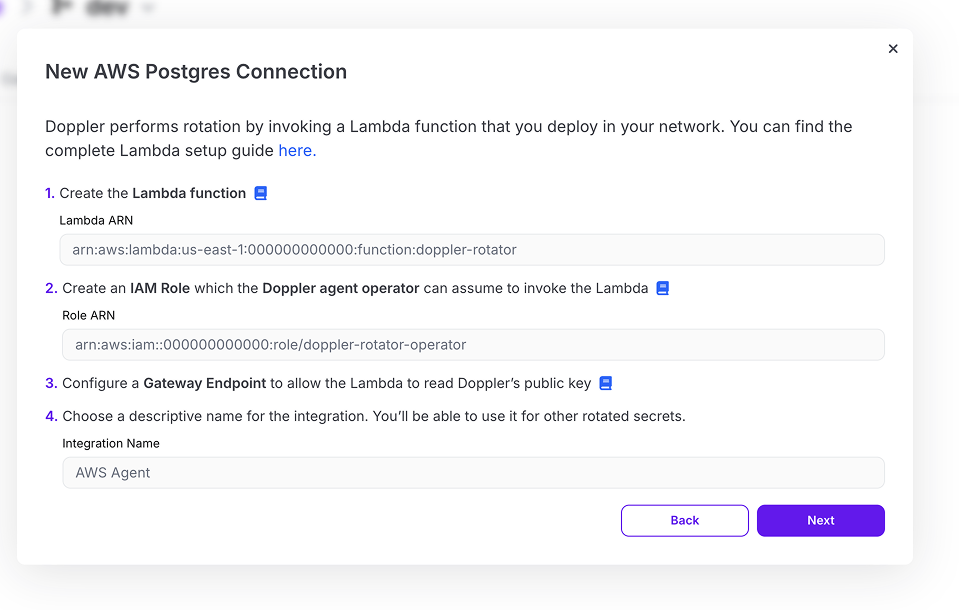
Lambda Proxy Setup
The Lambda proxy setup must be completed before the steps below
Overview
Once you've configured a Lambda proxy, the Postgres database rotation setup can be completed by providing the following properties, each of which are covered in more detail below:
- Database Rotation Configuration: The rotated secret name - which prefixes each individual secret - and the rotation interval
- Database Settings: Connection details used by the Lambda function to connect to your database
- Managing User Credentials: Username and password used by the Lambda function to connect to the database and rotate a user's password
- Users: Postgres users whose passwords are rotated
Configuration and Database Settings
- Rotated Secret Name: The name of the rotated secret object; it will also prefix each of the secrets that Doppler injects into your config. For example, if
DB_USERis entered, the following secrets would be injected into your config:DB_USER_HOSTDB_USER_PORTDB_USER_DATABASEDB_USER_USERNAMEDB_USER_PASSWORD
- Interval: How often your Postgres users' passwords are rotated
- Postgres Host: The hostname or IP of your Postgres database
- Postgres port:The port to connect on for your Postgres database. Defaults to 5432.
SSL Configuration
When the force_ssl parameter group option is set to true (which is the default in PG 15+ on AWS),
Doppler's lambda rotator must be given an SSL CA to use for its connection to the database.
In your RDS instance's connectivity section, you will see a Certificate authority field. By default,
this field will point to AWS's CA, e.g. rds-ca-rsa2048-g1. The required certificate can be found
on Amazon's documentation here
Download the non-global region-specific .pem file and paste its contents into the SSL CA
field in Doppler when creating your rotated secret.
Managing User
Postgres user that the Lambda function utilizes to connect to the Postgres database and update each secret instance's password at rotation time. The managing user's credentials are passed to your Lambda function at invocation time.
Requirements
- The managing user should be a new database user and not a user already in use
- The managing user must be able to update the passwords for each Postgres user instance
Once the managing user is created and entered in Doppler, its password should not be stored anywhere - it should not be used in any other locations.
Users
During the rotation process, Doppler rotates between the Postgres users you provide during the rotation configuration process. By providing the users to Doppler, Doppler doesn't need the ability to create new users - just update user passwords.
There are no requirements related to the users you provide except that that the managing user must be able to update their password.
Updated about 1 month ago
