GCP Secret Manager
reading time 3 mins
This guide will show you how to set up automatic syncing of Doppler secrets to GCP Secret Manager.
Prerequisites
- You have a GCP account and are familiar with GCP Secret Manager
- You have the gcloud CLI installed and authenticated
- You have enabled the Secret Manager API for your GCP project
IAM Service Account
Ensure gcloud is configured to use the correct project, e.g.
gcloud config set project yodaspeakbefore proceeding.
We need to set up a Service Account so Doppler has the required permissions to sync secrets to GCP Secret Manager.
- Adjust the
SECRET_PREFIXas desired - this limits Doppler's access to only GCP Secrets starting with this prefix. - The prefix may only contain alphanumeric characters, dashes, and underscores - a dash is recommended for the last character.
This is best done using the gcloud CLI:
# To narrow permission scope use this prefix for Doppler accessible secrets, adjust as desired
# This should match the prefix you enter in Doppler when setting up your integration
SECRET_PREFIX="doppler-";
# Get current project
PROJECT_ID="$(gcloud config get-value project --quiet)";
# Create a new Service Account
gcloud iam service-accounts create doppler-secret-manager \
--description="Service account for Doppler to sync secrets to Secret Manager" \
--display-name="Doppler Secret Manager";
# Attach SecretManagerAdmin policy to the new service account
gcloud projects add-iam-policy-binding $PROJECT_ID \
--member="serviceAccount:doppler-secret-manager@$PROJECT_ID.iam.gserviceaccount.com" \
--role="roles/secretmanager.admin" \
--condition="expression=resource.name.extract(\"secrets/{rest}\").startsWith(\"$SECRET_PREFIX\"),title=\"$SECRET_PREFIX*\"";
Then we create a new key for the service account to generate the required credentials for Doppler:
# Generate a key for your new service account
gcloud iam service-accounts keys create iam-key.json \
--iam-account="doppler-secret-manager@$PROJECT_ID.iam.gserviceaccount.com";
# Print (and then remove) the JSON credentials
cat iam-key.json && rm iam-key.json;
Copy the JSON credentials output in your shell as you'll need it for the next step.
Authorization
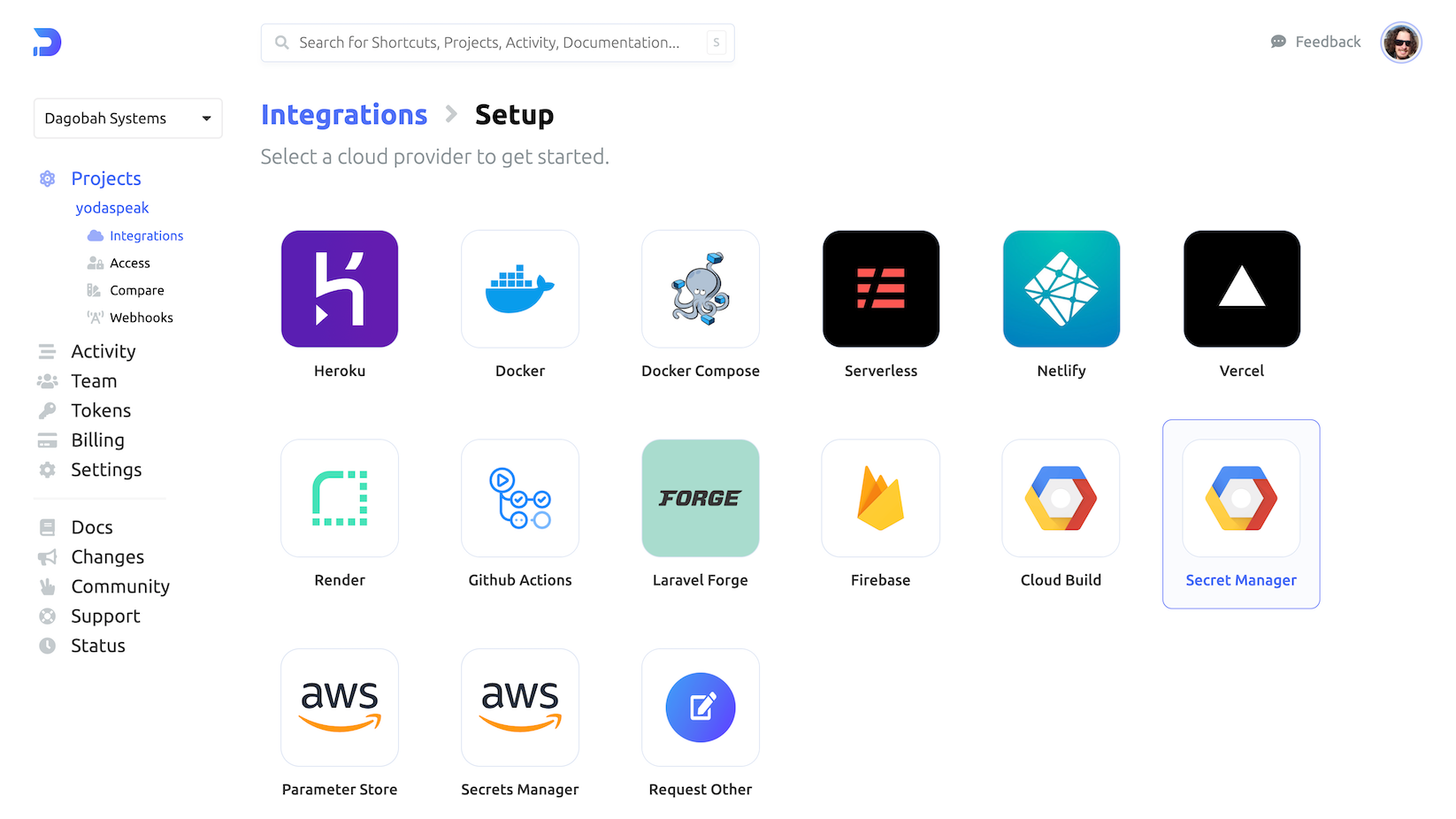
Navigate to the project you would like to integrate, click Integrations from the Projects menu, then select GCP Secret Manager to begin the authorization process.
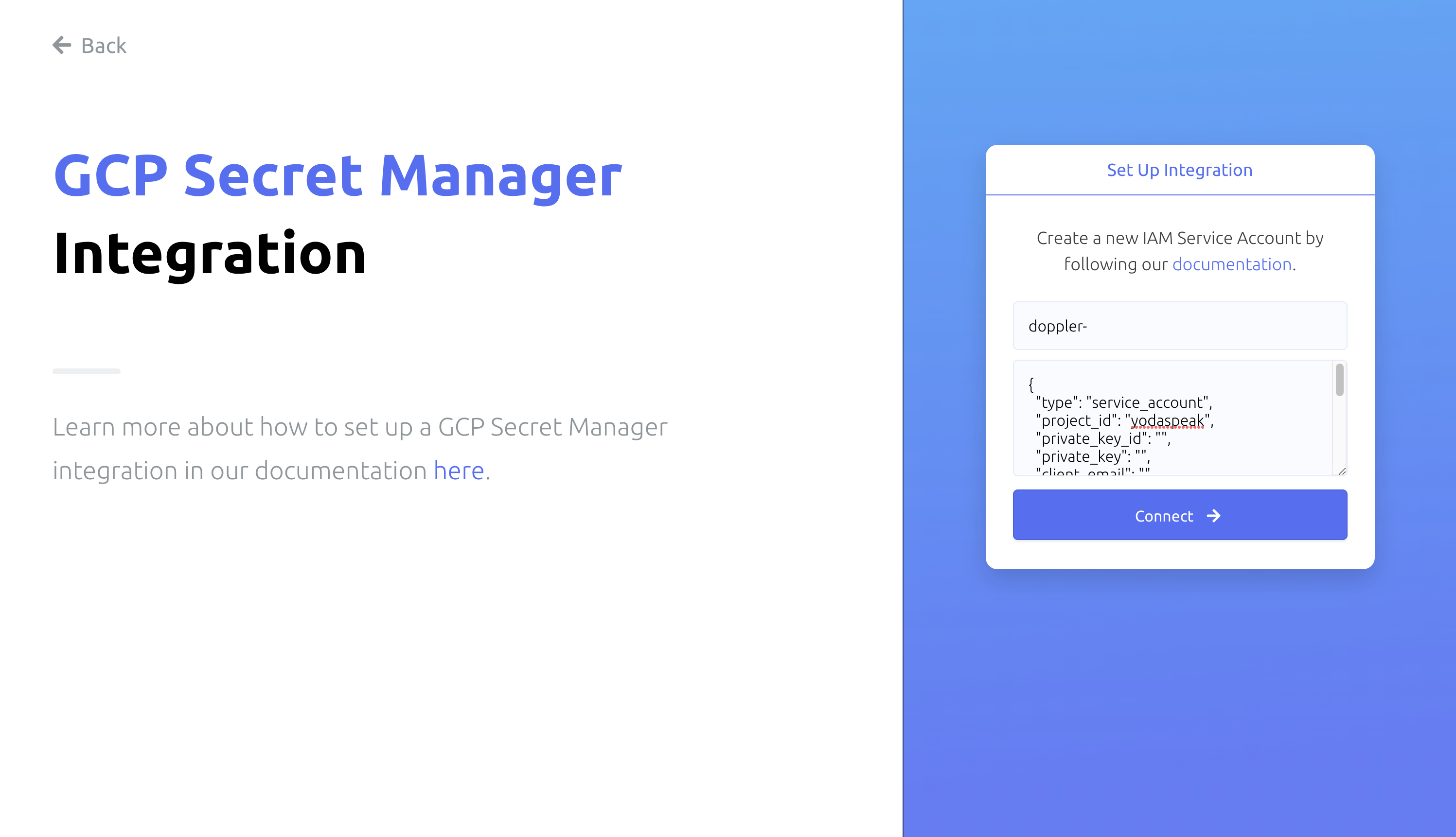
Enter the prefix used above (e.g., "doppler-"), paste the JSON from the shell into the credentials text field, then click Connect.
Configuration
Now chose the config to sync, the Region(s), and the enter a secret Name.
For region, Automatic replication is recommended, but you can instead specify which regions secrets should be replicated to. Learn more in the GCP Secret Manager replication docs.
Enter a Name (alphanumeric characters, dashes, and underscores) which will be concatenated to the prefix to display the Secret Manager Name (the GCP secret where Doppler will sync your secrets).
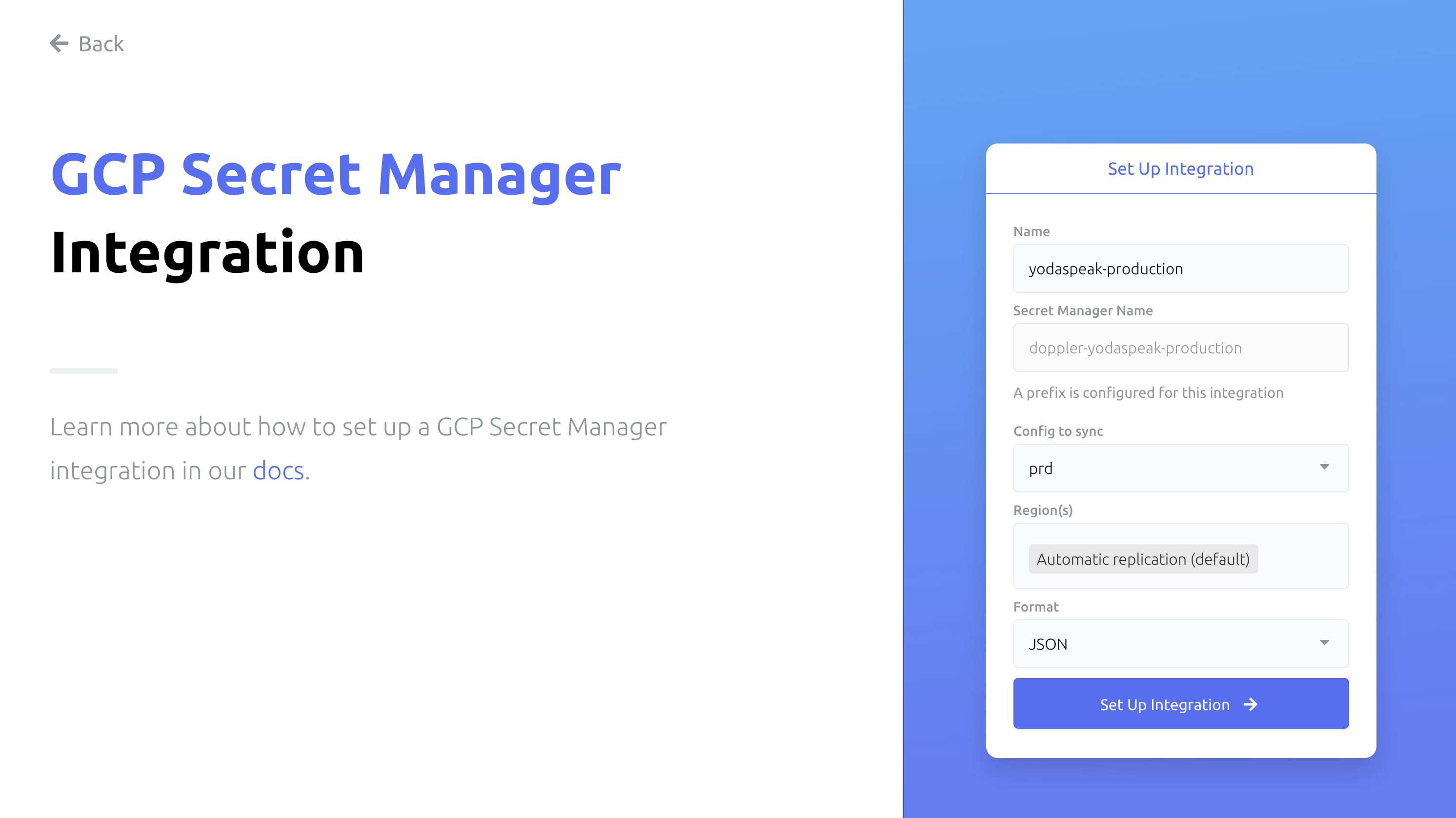
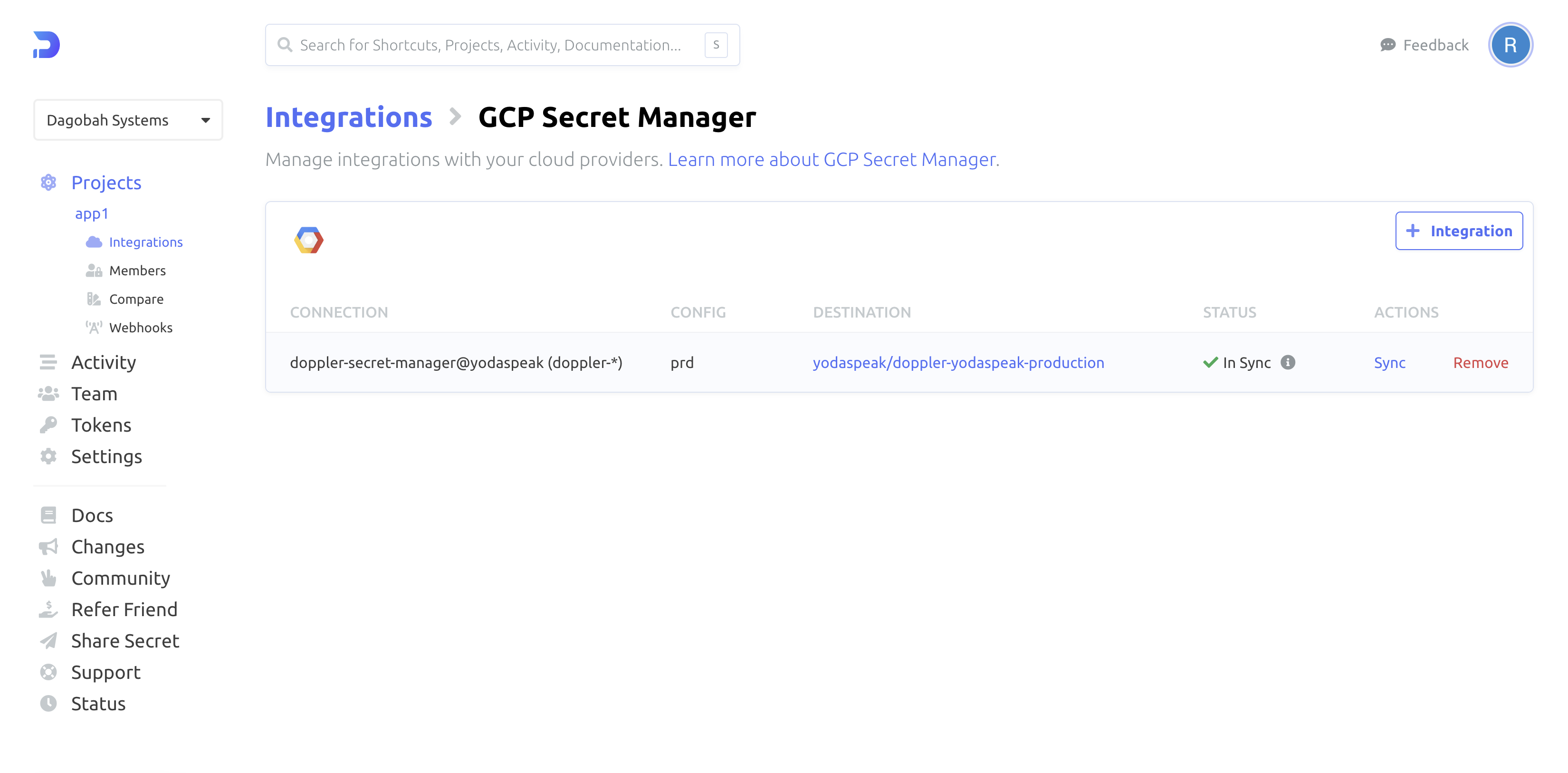
Click "Setup Integration" and you're all set! Click the DESTINATION link in the table to see your secrets in the GCP console.
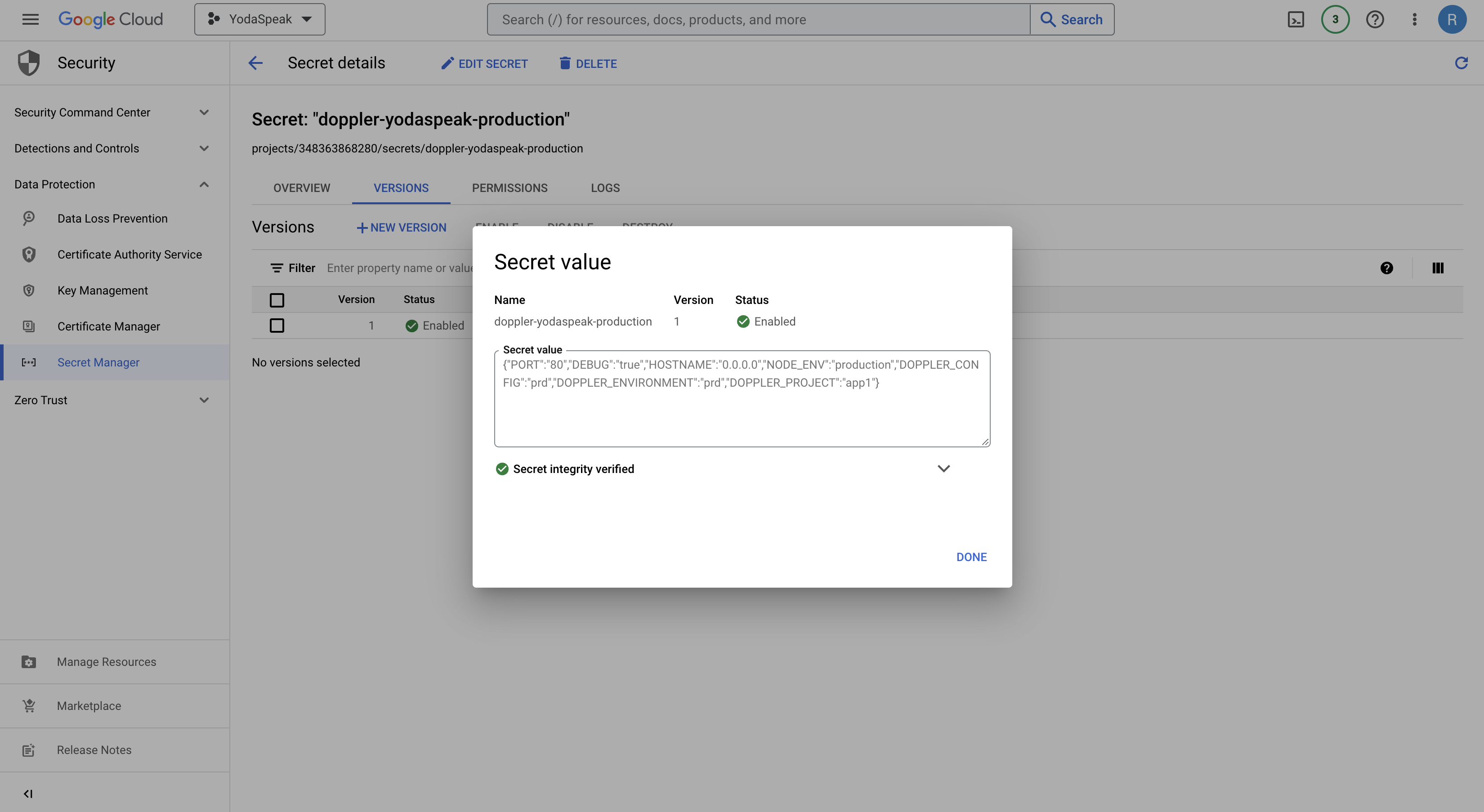
Doppler sync and secret versions
Every time a secret is changed in Doppler, this will create a new version of the secret in GCP Secret Manager, so ensure sure your code always retrieves the latest version using
/versions/latest.
Amazing Work!
You've successfully set up the Doppler GCP Secret Manager integration! Every time you update your secrets in Doppler, we will automatically sync them to GCP Secret Manager, creating a new version of that secret.
Updated 4 months ago
