AWS Parameter Store
Sync environment variables to AWS Parameter Store.
This guide will show you how to set up automatic syncing of Doppler secrets to AWS Parameter Store.
Prerequisites
- AWS Console Access
- AWS IAM access
- Ability to create IAM roles and Policies
- Ability to access IAM users
Authorization
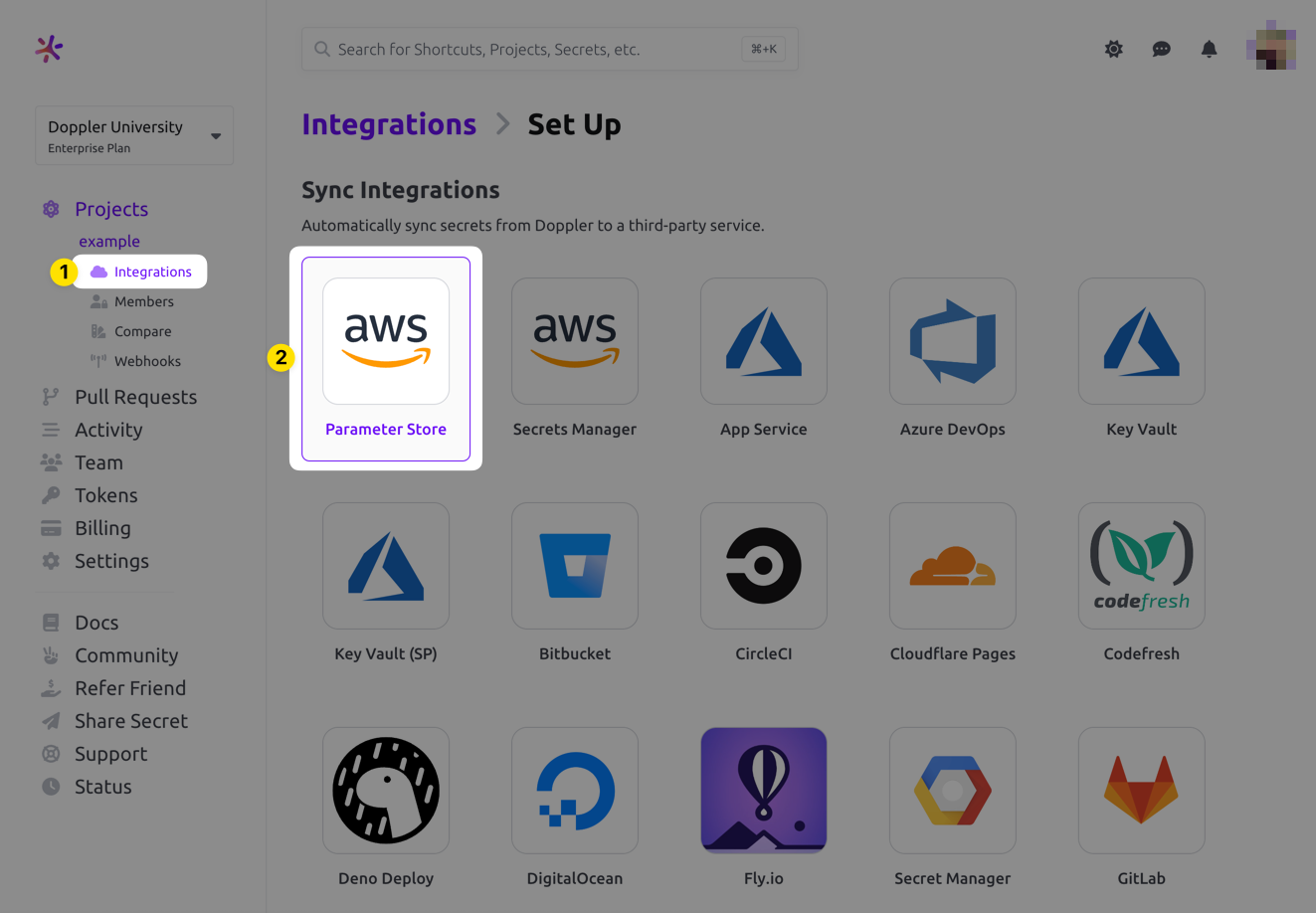
Navigate to the project you would like to integrate, click Integrations from the Projects menu, then select AWS Parameter Store to begin the authorization process.
If this is your first time setting up an integration with AWS Secrets Manager, you'll see the following screen
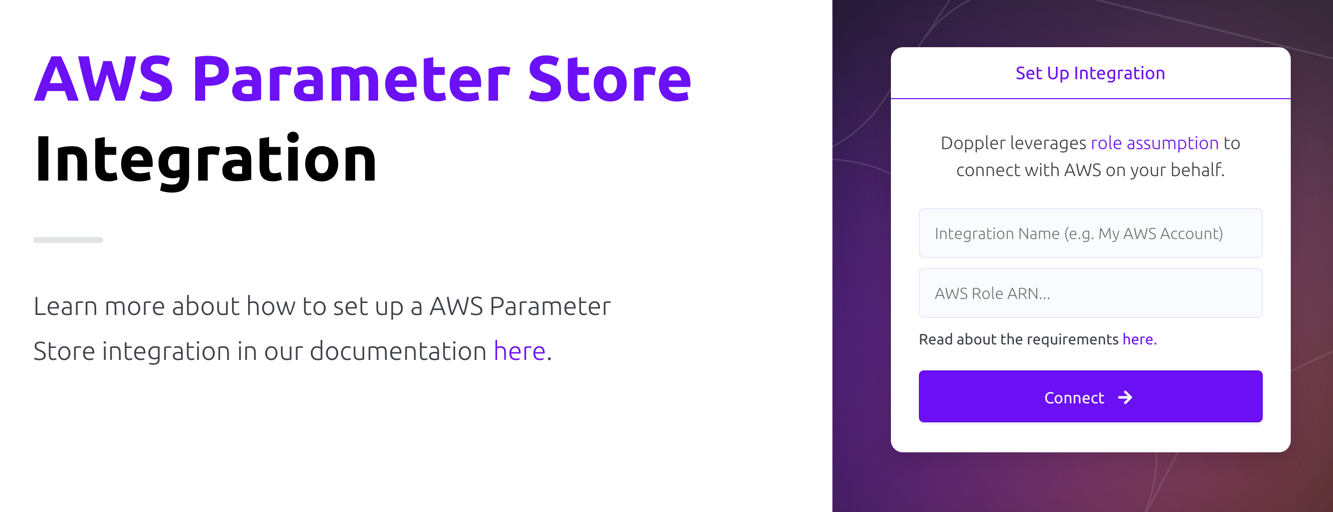
- Integration Name: A descriptor for the integration that will be displayed throughout Doppler
- AWS Role ARN: ARN for the role that Doppler will use to assume into your AWS account. Instructions are covered below
Role Assumption
Doppler uses an IAM role you provide to assume into your account. The role will leverage the policy below.
Policy
- Navigate to the Create New Policy section in the AWS IAM console
- Switch to the JSON tab
- Enter the following policy
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "AllowSSMAccess",
"Effect": "Allow",
"Action": [
"ssm:PutParameter",
"ssm:LabelParameterVersion",
"ssm:DeleteParameter",
"ssm:RemoveTagsFromResource",
"ssm:GetParameterHistory",
"ssm:AddTagsToResource",
"ssm:GetParametersByPath",
"ssm:GetParameters",
"ssm:GetParameter",
"ssm:DeleteParameters"
],
"Resource": "*"
}
]
}
- Optionally provide tags
- Name your policy and hit create
Role
- Navigate to the create role section of the AWS IAM console
- Select AWS account for the Trusted entity type
- Select Another AWS account under An AWS account
- Enter 299900769157 for the Account ID. This is Doppler's account ID.
- Under Options check Require external ID
- Enter your workplace slug for the External ID. You can obtain your workplace slug by visiting the Doppler dashboard. In the URL, grab the value after
/workplace/ - Leave require MFA unchecked
- Enter your workplace slug for the External ID. You can obtain your workplace slug by visiting the Doppler dashboard. In the URL, grab the value after
- Attach the policy you created above.
- Complete the role setup. When the role is created, click the link to it to view its details
- Copy its ARN
Configuration
AWS Parameter Store requires that all parameters have a value, so any secrets with an empty string value will not be synced over.
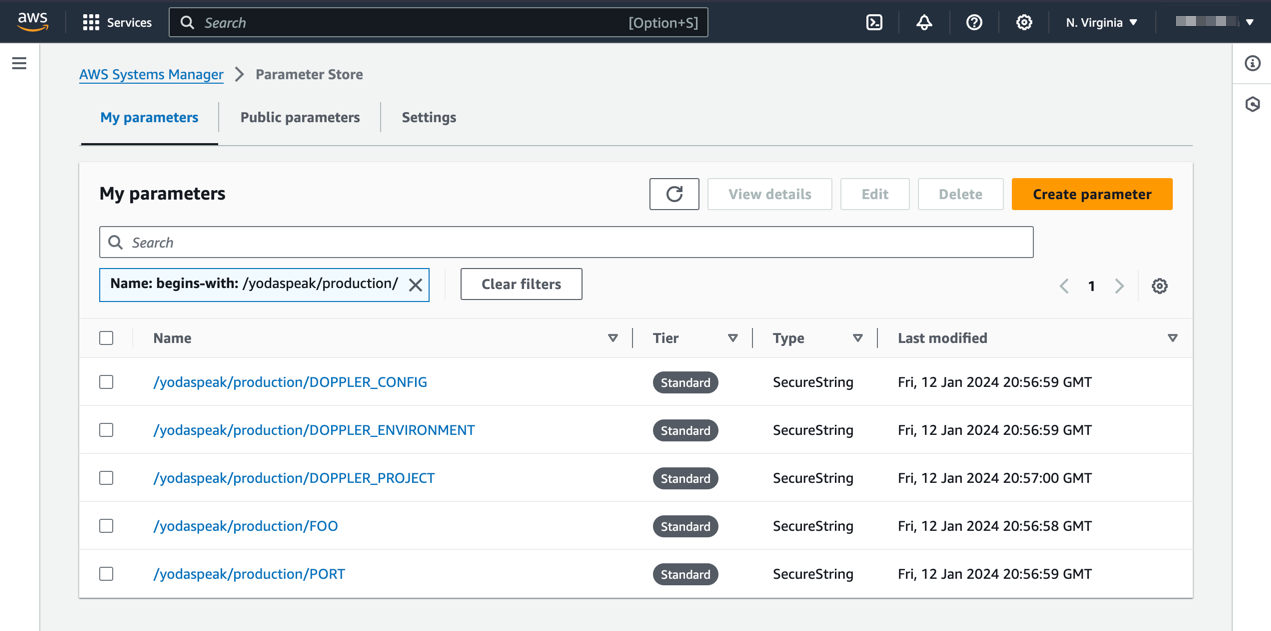
Now chose the config to sync, the AWS region, and optionally, the Path that acts as a prefix for the name of each secret synced. For example, a Path value of /your-app/production/ with a secret named API_KEY would result in a Parameter Store key of /your-app/production/API_KEY.
Options
Save as Secure String
We recommend saving your Doppler secrets as Secure Strings. However, for services like CloudFormation, secure secrets are not supported. In that case, you can uncheck this box to save your secrets in plain text. We only recommend this for configuration variables.
Tags
The list of tags to be applied to each parameter resource.
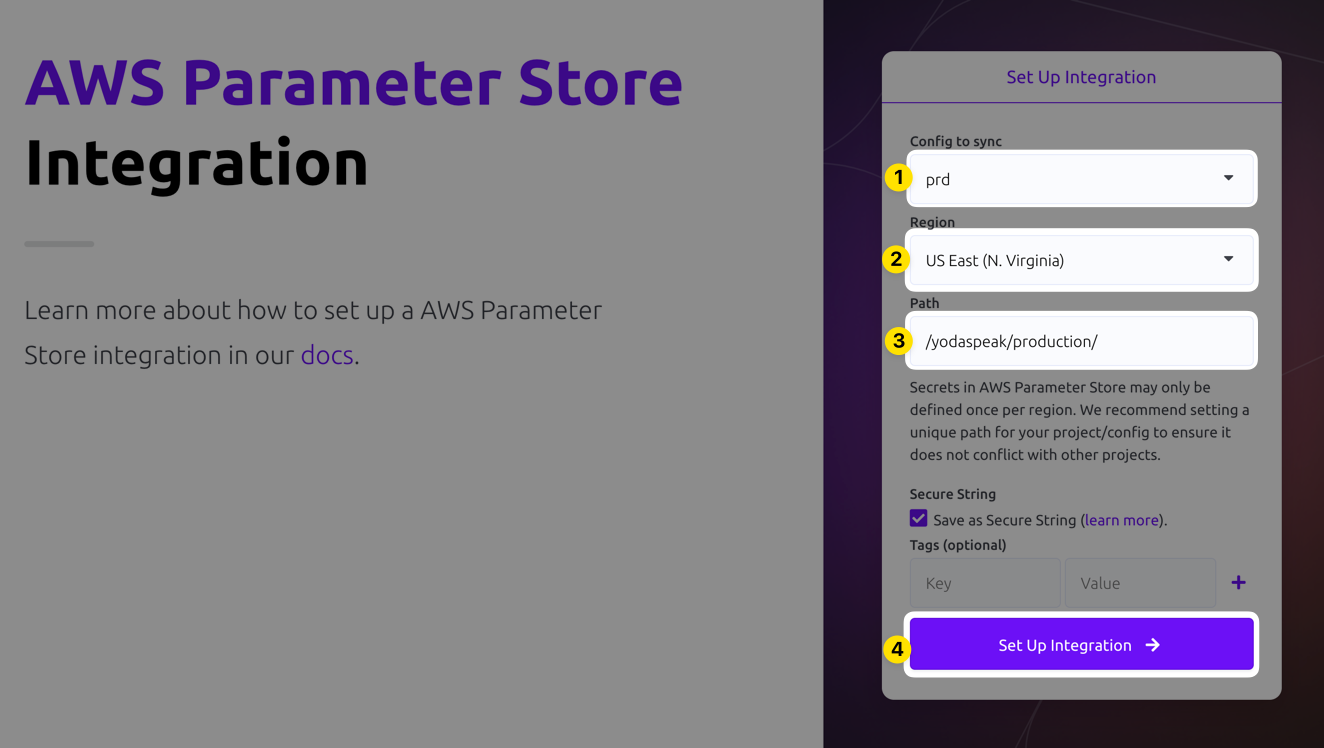
Click Set Up Integration and Doppler will instantly sync your secrets to AWS! To confirm the integration is working correctly, you can view the synced secrets in Parameter Store by clicking the DESTINATION link
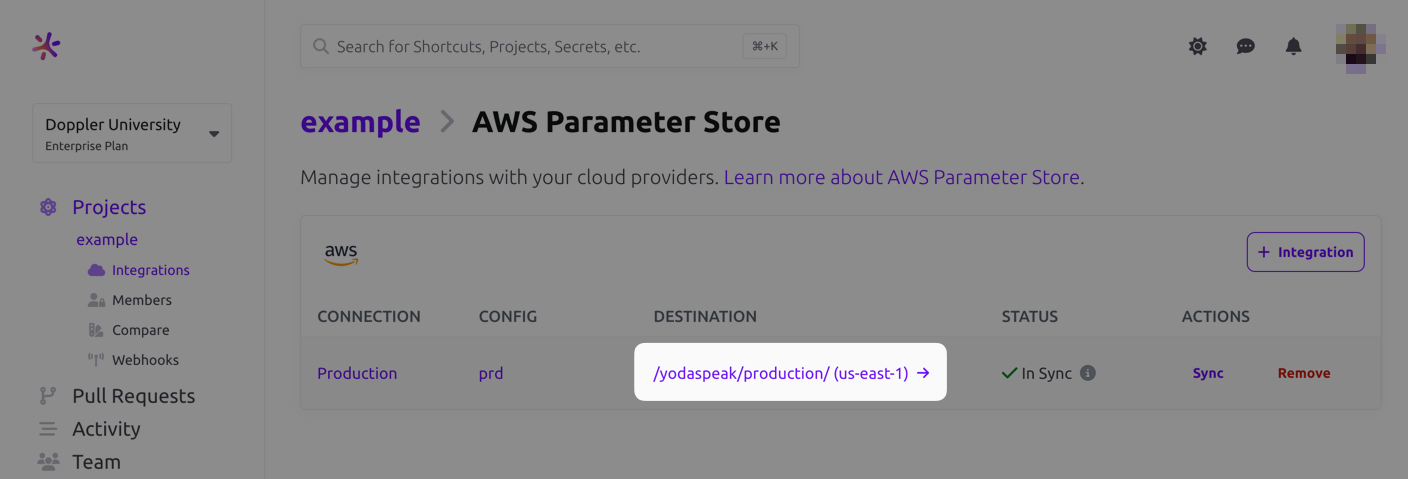
Amazing Work!
You've successfully set up the Doppler AWS Parameter Store integration! Every time you update your secrets in Doppler, we will automatically update them to AWS Parameter Store.
Importing Parameters
The AWS Parameter Store integration doesn't support importing parameters, but you can still manually import those into Doppler fairly easily using a combination of the AWS CLI and the Doppler CLI! Assuming your parameters are stored in a format similar to /some/path/PARAM_NAME, then you can do the following:
PROJECT_NAME=your-doppler-project-name
CONFIG_NAME=your-doppler-config-name
AWS_PARAM_STORE_PATH=/some/path
doppler secrets upload -p $PROJECT_NAME -c $CONFIG_NAME <(aws ssm get-parameters-by-path --path $AWS_PARAM_STORE_PATH --with-decryption | jq '.Parameters[] | { (.Name | split("/") | last): .Value }' | jq -s add)
This pulls the AWS Parameters from the designated path as JSON, then manipulates the JSON result into a format the Doppler CLI expects. It then feeds that output into doppler secrets upload to the project and config you specify.
Updated 7 months ago
